What is AutoSIEM?
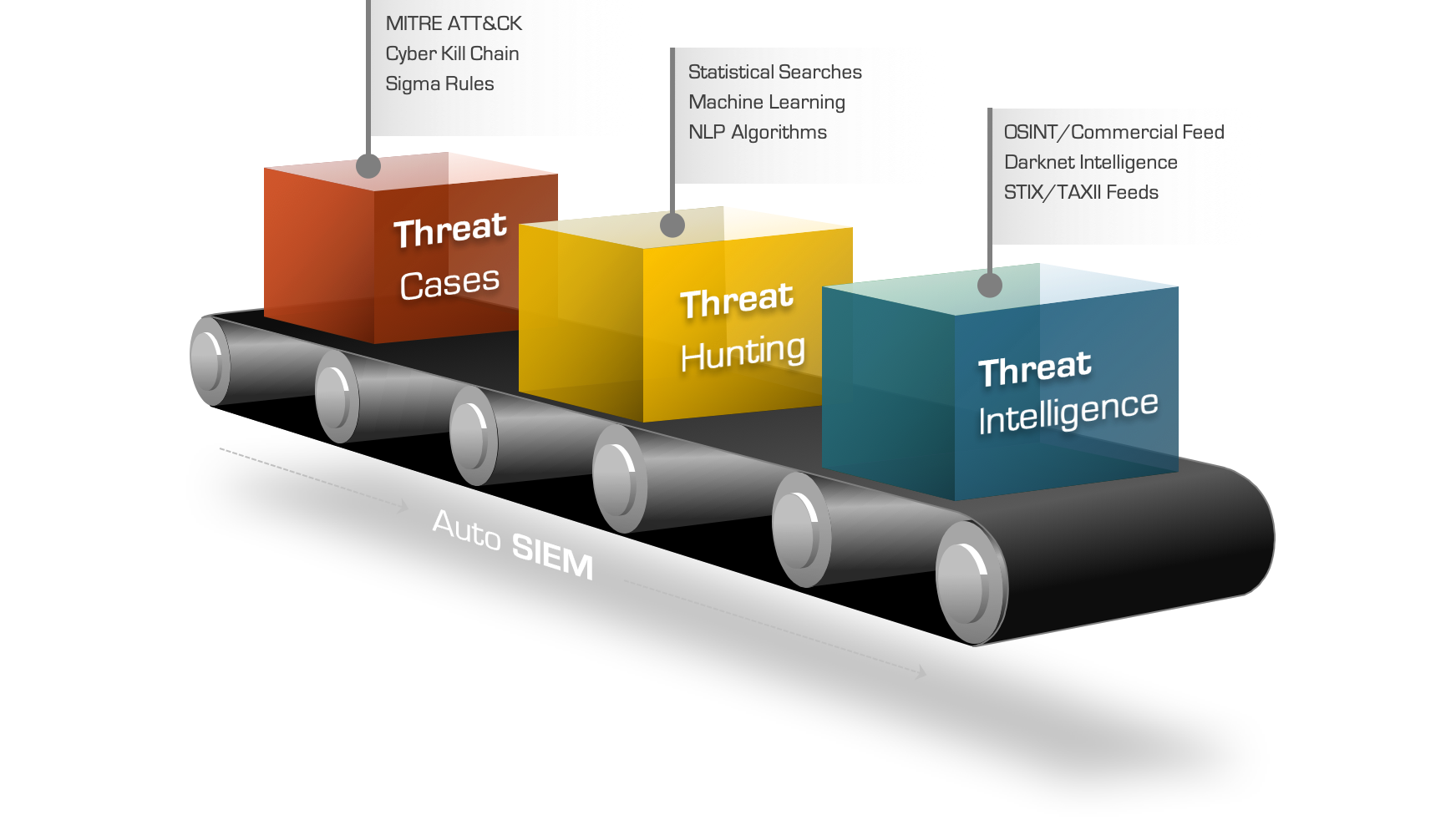
AutoSIEM is an AI-driven security automation platform built for large-scale Security Operations Centers. It integrates with leading enterprise SIEM environments to automate threat correlation reducing manual analyst workload while delivering faster, more accurate threat detection.
AutoSIEM collects and correlates security events from across your environment including endpoints, applications, network devices, and security tools and applies over 1,000 continuously tuned detection rules to surface real threats with minimal noise.
AutoSIEM is designed to be nearly maintenance-free. Its machine learning engine continuously tunes detection rules automatically so your SOC stays current with the evolving threat landscape without constant manual updates.
How It Works
1
Security Events Ingested
AutoSIEM collects security events from across your environment endpoints, firewalls, routers, applications, antivirus, and other security tools through your existing SIEM infrastructure.
2
Threat Intelligence Applied
Ingested events are enriched with Eunomatix Threat Intelligence (ETI) feeds, continuously updated by a team of expert security engineers and exploit researchers monitoring the global threat landscape.
3
Correlation Rules Executed
Over 1,000 static correlation and statistical detection rules aligned to MITRE ATT&CK Tactics, Techniques, and Procedures are applied to identify both known and emerging threat patterns.
4
ML Models Detect Anomalies
A custom machine learning framework runs in parallel, detecting behavioral anomalies and zero-day threats that signature-based rules alone would miss.
5
Alerts Surfaced & Auto-Tuned
High-fidelity alerts are surfaced to SOC analysts. AutoSIEM continuously tunes its own detection rules based on feedback and evolving threat data reducing false positives over time.
Core Features
AI & GenAI Threat Detection
Combines traditional correlation with AI and Generative AI techniques to detect zero-day threats and novel attack patterns.
MITRE ATT&CK Alignment
All detection rules are mapped to MITRE ATT&CK TTPs, covering both pre-compromise and post-compromise attack stages.
1,000+ Correlation Rules
A comprehensive library of static, statistical, and ML-based correlation rules continuously maintained and auto-tuned by the platform.
Machine Learning Framework
A purpose-built ML detection engine identifies behavioral anomalies and supports threat hunting and MLOps workflows for SOC teams.
Horizontal Scalability
Designed to scale across very large security operations handling high event volumes without compromising detection performance.
Multi-Tenancy Support
Supports logical customer and business unit segregation making it ideal for MSSPs and enterprises with complex organizational structures.
Eunomatix Threat Intelligence
Bundled ETI feeds, continuously updated by Eunomatix security researchers, enrich detections with current adversary infrastructure and indicators.
SIEM Integration
Integrates with enterprise SIEM platforms to automate threat correlation within your existing security infrastructure no rip-and-replace required.
Compliance & Standards
AutoSIEM's MITRE ATT&CK-aligned detection library and comprehensive audit logging help enterprises demonstrate security control coverage across major regulatory and compliance frameworks.
MITRE ATT&CK
SOC 2
ISO 27001
NIST CSF
PCI DSS
HIPAA Ready
AutoSIEM's detection rule library is built directly on MITRE ATT&CK Tactics, Techniques, and Procedures making it straightforward to map detected threats to specific compliance control requirements during audits and security assessments.