Zero-Day
Threat Detection
What is Logster?
Logster is an AI-driven threat detection platform that continuously ingests native operating system logs from Windows and Linux endpoints and analyzes them in real time to detect advanced threats, including zero-day attacks, beyond even traditional signatures.
Logster gives SOC teams high-confidence, MITRE ATT&CK-mapped alerts with full attack context, reducing alert fatigue and enabling faster incident response by processing OS-level telemetry directly, including kernel events, script execution logs, and system call activity.
Logster detects threats by learning what "normal" looks like on each host, so even unknown, fileless, and signature-evading attacks trigger high-confidence actionable alerts.
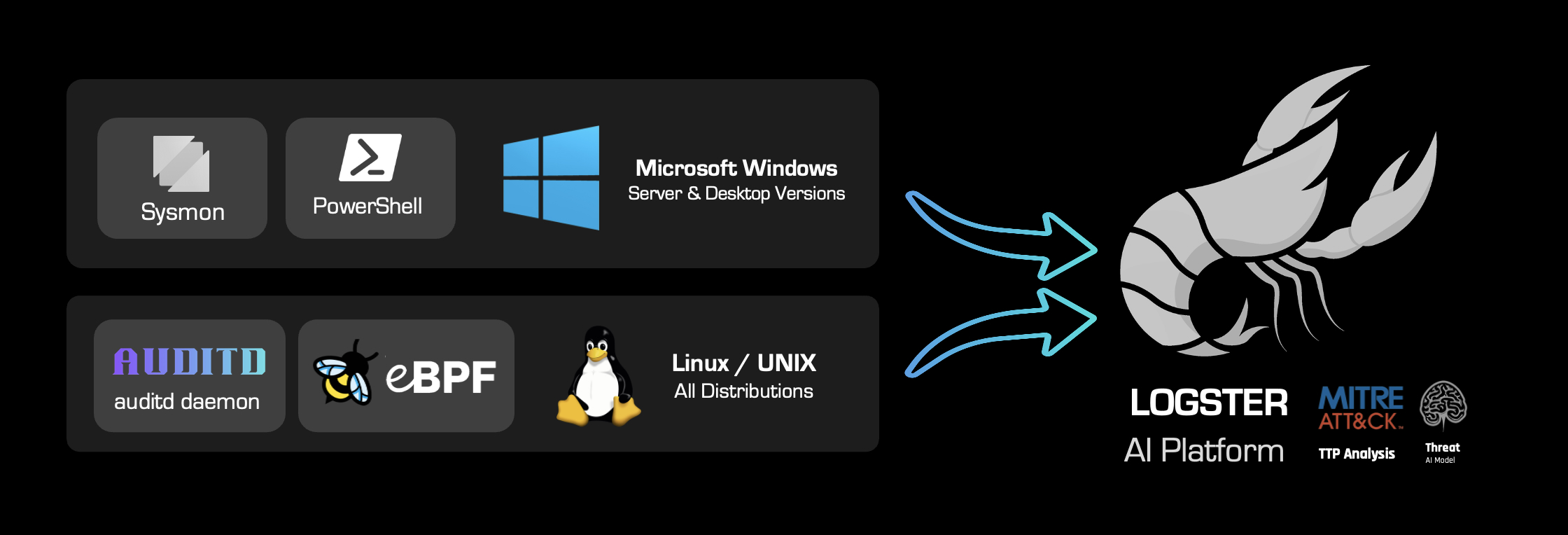
Operating System Coverage
Logster ingests native telemetry from the following OS log sources with no third-party agents or proxies required:
Windows Sysmon
PowerShell Operational Logs
Linux auditd
eBPF Kernel Telemetry
Windows Server 2016+
Linux Kernel 4.15+
What Logster Detects
Logster's behavioral engine is designed to surface threats that traditional security tools miss, particularly attacks that operate without known signatures.
Fileless Attacks
Detects attacks that execute entirely in memory or abuse legitimate OS tools leaving no file on disk for traditional antivirus to scan.
Suspicious Script Execution
Monitors PowerShell and scripting engine activity for obfuscated commands, encoded payloads, and anomalous execution patterns.
Privilege Escalation
Identifies unauthorized attempts to elevate process privileges or exploit OS vulnerabilities to gain elevated access on a host.
Lateral Movement
Correlates cross-host behavioral patterns to detect adversaries moving through the environment after initial compromise.
How It Works
1
Telemetry Collected at the OS Level
Logster collects native OS events directly from Windows (Sysmon, PowerShell) and Linux (auditd, eBPF) capturing process creation, system calls, script execution, and kernel-level activity with minimal overhead.
2
Telemetry Streamed in Real Time
Encrypted telemetry is streamed directly to the Logster inference engine either cloud-hosted or on-prem with sub-second response, ensuring detection keeps pace with active attacks.
3
Behavioral Baselines Established
The AI engine builds per-host behavioral profiles by continuously learning normal operating patterns allowing it to distinguish legitimate admin activity from malicious deviations with high accuracy.
4
Multi-Dimensional Analysis Applied
Events are correlated across time, users, and hosts using a hybrid detection engine combining machine learning models, behavioral analysis, and temporal attack sequence analysis.
5
Enriched Alerts Delivered to SOC
High-confidence, MITRE ATT&CK-mapped alerts are delivered to the SOC with full process lineage, attack timelines, and risk scores enabling analysts to immediately understand the scope and stage of an incident.
Core Features
Real-Time Log Streaming
Native OS telemetry is streamed directly to the inference engine with sub-second latency eliminating detection lag from batch processing.
Hybrid AI Detection Engine
Combines machine learning models, behavioral baselining, and curated detection logic to surface high-confidence threats while minimizing false positives.
MITRE ATT&CK Mapping
Every alert is mapped to specific MITRE ATT&CK tactics and techniques giving analysts immediate context on attack type, stage, and recommended response.
Per-Host Behavioral Baselining
Individual behavioral profiles are built for every monitored host enabling localized anomaly detection without generating global false positives.
Temporal Attack Correlation
Multi-stage attack campaigns are identified by correlating telemetry events across time exposing attacker intent from initial access through to exfiltration.
Risk-Based Alert Scoring
Alerts are scored by correlating threat severity with model confidence prioritizing the highest-risk sequences so analysts address the most critical incidents first.
Flexible Deployment
Deploy as a cloud-hosted SaaS, private cloud instance, or fully on-prem inference node including support for air-gapped environments with no internet dependency.
Data Security & Privacy
All telemetry is encrypted in transit. On-prem deployments keep all data within your own infrastructure with an optional zero-log mode for strict privacy requirements.
Compliance & Standards
Logster's MITRE ATT&CK-aligned detections and comprehensive OS audit trails help enterprises demonstrate security coverage across major compliance frameworks and support rapid response to audit inquiries.
MITRE ATT&CK
SOC 2
ISO 27001
NIST CSF
HIPAA Ready
PCI DSS
See Logster in Action
Explore the full product capabilities, pricing, and deployment options on the Logster platform.
Visit Logster